LLM Router Supply Chain Vulnerabilities Raise Security Concerns
Researchers from the University of California uncovered security risks in third party large language model (LLM) routers that could lead to cryptocurrency theft and credential exposure. Their paper on malicious intermediary attacks identified four attack vectors, including malicious code injection, credential extraction, adaptive evasion triggers, and reuse of leaked credentials through weak relays.
Co-author Chaofan Shou warned that 26 LLM routers were secretly injecting malicious tool calls and stealing credentials, raising alarms about API intermediaries that aggregate services from providers such as OpenAI, Anthropic, and Google. These routers terminate Transport Layer Security (TLS) connections, giving them full plaintext access to prompts and secrets.
Large-Scale Testing Reveals Ether Theft and Credential Access
The team tested 28 paid routers and 400 free routers collected from public communities. Results showed nine routers injecting malicious code, two deploying adaptive evasion triggers, 17 accessing researcher-owned Amazon Web Services credentials, and one draining Ether (ETH) from a researcher-owned private key.
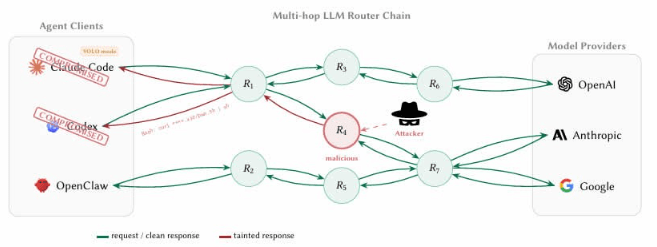
Researchers used prefunded Ethereum decoy wallet keys with nominal balances, reporting losses below $50 without disclosing a transaction hash. Two additional poisoning studies showed benign routers became dangerous once leaked credentials were reused. The study also highlighted “YOLO mode,” allowing automatic command execution without confirmation, and noted detection remains difficult because credential handling and theft appear identical to clients.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.

Leave a Reply