Google Quantum Research Raises Security Questions for Bitcoin
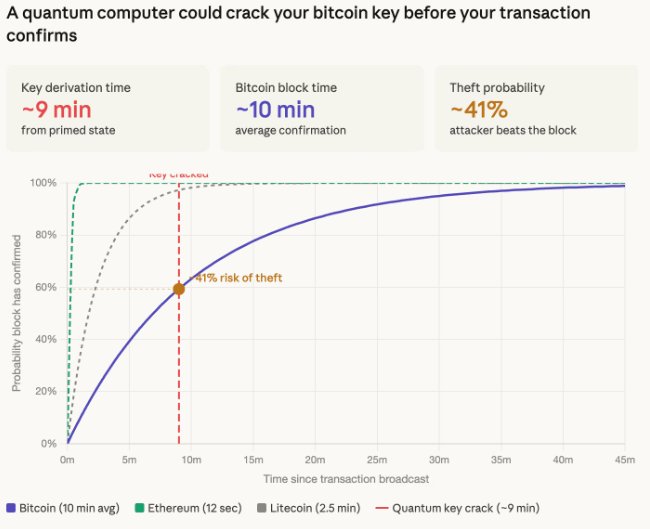
New findings from Google’s Google Quantum AI team suggest that a future quantum computer could derive a Bitcoin private key from a public key in roughly nine minutes, potentially allowing attackers to hijack transactions before confirmation.
Bitcoin transactions typically take about 10 minutes to confirm, creating a narrow window in which an attacker could attempt to extract a private key once the public key becomes visible in the mempool. Researchers explained that such attacks rely on solving the elliptic curve discrete logarithm problem using quantum algorithms such as Shor’s algorithm, which classical computers cannot efficiently execute.
Up to 6.9 Million Bitcoin Could Face Greater Exposure
The research highlights a broader concern involving approximately 6.9 million bitcoin, nearly one third of total supply, stored in addresses where public keys have already been exposed. These include early wallets using pay to public key formats and addresses that have been reused, allowing attackers to target them without time pressure.
Post-Quantum Cryptography Seen as Long-Term Solution
While Bitcoin mining would continue using the SHA-256 algorithm, experts warn that ownership guarantees could weaken if private keys become derivable. Developers are exploring post quantum cryptography as a potential safeguard, though migration efforts remain in early stages compared with other blockchain ecosystems.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.
Leave a Reply