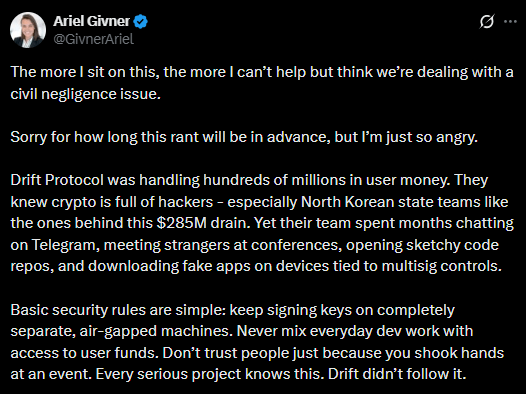
The recent $280 million exploit involving Drift Protocol may qualify as civil negligence, according to Ariel Givner, who reviewed the project’s post-incident update. She explained that civil negligence occurs when a platform fails to meet its basic duty to safeguard user funds.
Givner stated that the Drift team allegedly ignored standard operational security practices, including keeping signing keys on separate air-gapped systems and performing proper background checks on developers met during industry events. She also noted that developers reportedly communicated with unknown individuals via Telegram, opened suspicious code repositories, and downloaded unverified applications on devices connected to multisignature controls.
Months-Long Attack Linked to North Korea Threat Actors
According to the Drift team, attackers began building relationships with developers at a major crypto conference in October 2025. Over the next six months, they established trust before sending malicious links that installed malware on developer machines.
The incident is believed to be connected to Lazarus Group, the same actors suspected in the October 2024 Radiant Capital hack. Reports indicate that advertisements for potential class-action lawsuits against Drift Protocol have already begun circulating following the breach.
Disclaimer
This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency trading involves risk and may result in financial loss.

Leave a Reply